Synchronised SNES Bikes to Troll’s Nest
Reprogramming SNES games on the fly, Modelling bike sketches, and Feeding the Trolls. These and many other stories on this week
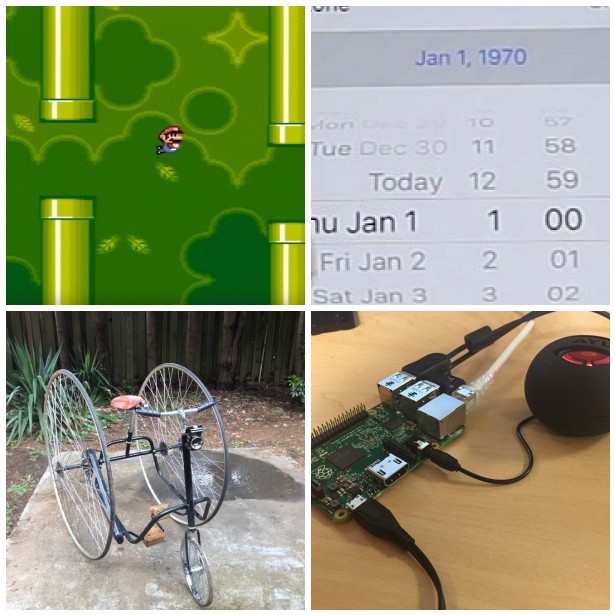
SNES Code Injection Notes
This document is intended to be used as notes for completing the SNES code injection exploit. It doesn
US anti-encryption law is so 'braindead' it will outlaw file compression
Meanwhile, in the technical world, experts have been going through the legislation and pointing out glaring holes in the draft bill. Bruce Schneier, the guy who literally wrote the books on modern cryptography, noted that the bill would make most of what the NSA does illegal, unless No Such Agency is willing to backdoor its own encrypted communications.
“This is the most braindead piece of legislation I’ve ever seen,” Schneier
What does a bike look like?
I decided my job was going to be presenting the potential and the beauty inside these sketches. I selected those that I found most interesting and genuine and diverse, then rendered them as if they were real. I became the executor of these two minute projects by people who were mainly non-designers and confirmed my suspicion: everyone, regardless his age and job, can come up with extraordinary, wild, new and at times brilliant inventions.
Some more awesome bikes:

Built by Hiwheel

Built by Greg Merkley

Built by Greg Merkley
Should We Feed the Trolls?
In an essay last week, the writer Stephen Marche set out to explore a Reddit-hosted community that has a reputation for being one of the most misogynistic swamps on the Internet. Marche
Apple Ends Support for QuickTime for Windows; New Vulnerabilities Announced
Computers running QuickTime for Windows will continue to work after support ends. However, using unsupported software may increase the risks from viruses and other security threats. Potential negative consequences include loss of confidentiality, integrity, or availability of data, as well as damage to system resources or business assets. The only mitigation available is to uninstall QuickTime for Windows. Users can find instructions for uninstalling QuickTime for Windows on the Apple Uninstall QuickTime page.
Nest Reminds Customers That Ownership Isn't What It Used to Be
Nest Labs, a home automation company acquired by Google in 2014, will disable some of its customers’ home automation control devices in May. This move is causing quite a stir among people who purchased the $300 Revolv Hub devices
iOS 1970 Bug Can Be Exploited via WiFi Networks
The iOS 1970 bug that can brick your devices is back and with a twist, with two security researchers now saying they were able to craft an automated exploit that can leverage the same issue via network connections, without needing access to a user’s phone.
Canadian Police Obtained BlackBerry’s Global Decryption Key
According to technical reports by the Royal Canadian Mounted Police that were filed in court, law enforcement intercepted and decrypted roughly one million PIN-to-PIN BlackBerry messages in connection with the probe. The report doesn’t disclose exactly where the key
Amazon Alexa on a Raspberry Pi
This project demonstrates how to access and test the Alexa Voice Service using a Java client (running on a Raspberry Pi), and a Node.js server. You will be using the Node.js server to get a Login with Amazon authorization code by visiting a website using your computer’s (Raspberry Pi in this case) web browser.
E16 S16

